Identify Critical Business Functions and Applications
-
Identify and Quantify Financial and Operational impact of loss of Business Services and Applications for each business area
-
Understand priority for recovery of critical business processes and applications based on criticality, time sensitivity, and dependencies
-
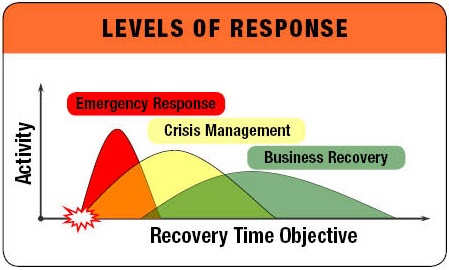
Identify Recovery Time Objectives (RTO) and Recovery Point Objectives (RPO) for each application/system
Risk Assessment
The Risk Assessment identifies man-made, technological, and natural threats that can adversely affect your key business and IT facilities. The study assesses probability and potential impact of each threat and level of mitigation.
Review Recovery Strategies With Management
Identify gaps in current Recovery strategies and recommend Availability strategies that meet the established Business requirements.
